Most cloud failures are not caused by technical limits.
They are caused by forgotten responsibility.
Across growing organizations, cloud sprawl rarely looks chaotic at first. Teams launch new accounts for testing. Separate environments are created for migration. Temporary integrations require cross-account access.
Each action is reasonable.
Over time, the problem is not complexity.
It is memory.
The Orphaned Account Pattern
An orphaned account does not mean abandoned infrastructure. It means unclear ownership.
A staging account remains active long after the product ships.
A sandbox created during experimentation still hosts running services.
A cross-account integration persists long after the original team reorganized.
Nobody deliberately ignores it.
But nobody explicitly owns it either.
This is where operational friction begins.
Security reviews surface unknown access patterns.
Finance questions unexplained cost lines.
Architects struggle to map dependencies during incidents.
When asked who is responsible, the answer becomes uncertain.
And uncertainty slows everything.
Why Tagging Is Not Enough
Many organizations attempt to solve ownership through tagging standards.
Tags are helpful.
They indicate cost centers, environments, or teams.
But tags do not explain:
Who last modified the resource
Whether the owning team still exists
If the access patterns changed over time
How the resource interacts with other accounts
Ownership is dynamic.
Tags are static.
Without change history tied to ownership context, orphaned resources quietly accumulate risk.
The Operational Cost
Fragmented ownership creates three predictable outcomes:
Delayed incident response
When no clear owner exists, escalation paths stall.
Audit friction
Compliance teams spend time identifying responsibility before addressing risk.
Silent cost leakage
Underutilized or forgotten resources continue consuming budget.
These costs rarely appear as a single catastrophic event.
They manifest as slow inefficiency.
And slow inefficiency compounds.
Rebuilding Cloud Memory
Solving fragmented ownership requires more than asset inventory.
It requires reconstructing change history across accounts.
Architects need visibility into how resources connect.
DevOps needs clarity on who modified what and why.
Security needs traceable access chains.
Finance needs alignment between infrastructure and accountability.
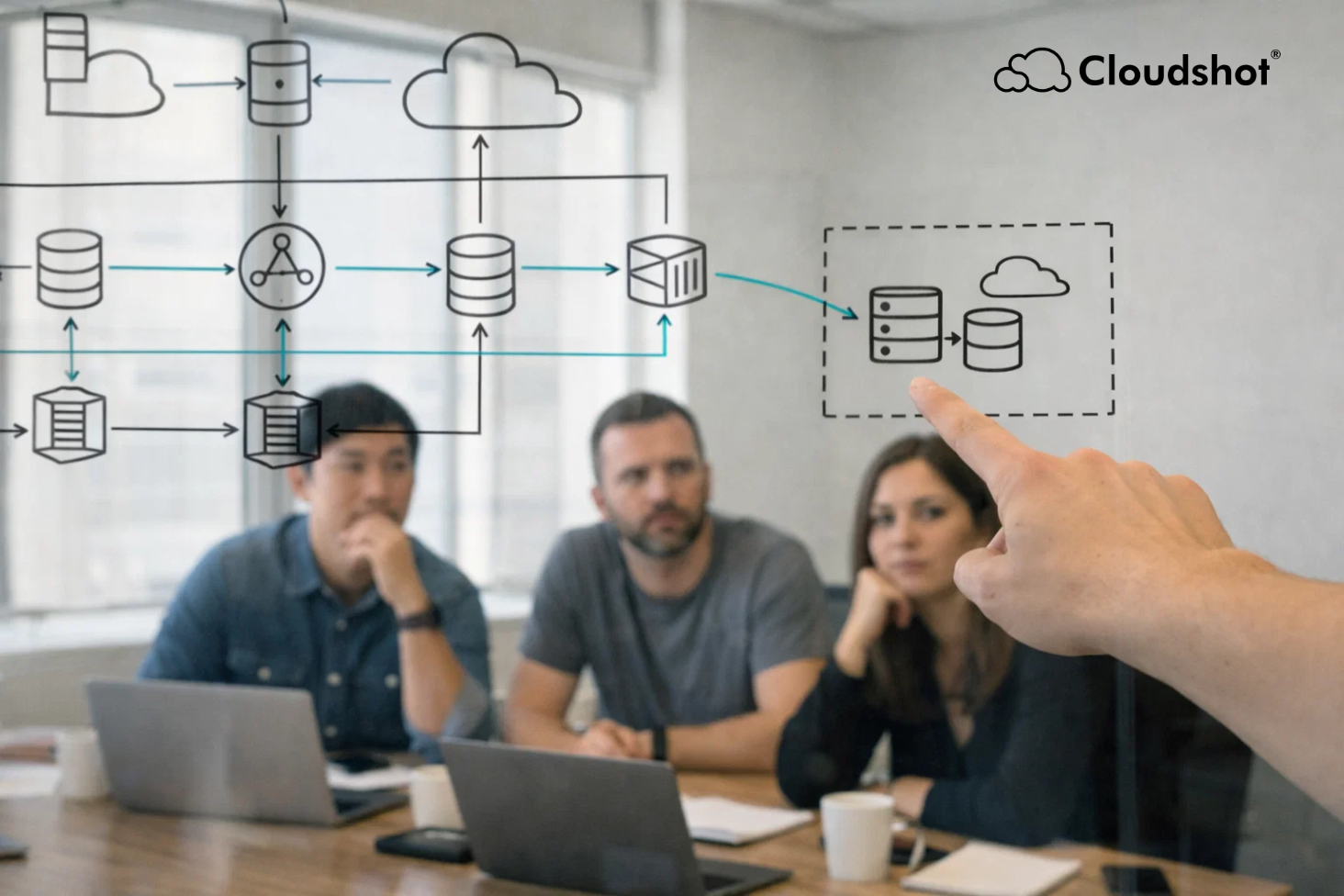
When cross-account resources are visualized within a unified map, orphaned accounts become visible immediately.
Not just as isolated infrastructure.
But as part of a broader dependency story.
Cloudshot approaches ownership through change narratives.
Instead of viewing accounts separately, it stitches activity, IAM updates, infrastructure changes, and runtime behavior into one readable timeline.
The result is simple.
Every resource has context.
Every account has traceability.
Every environment has an accountable owner.
And memory returns to the system.
Accountability as Infrastructure Discipline
Cloud maturity is not measured by the number of accounts.
It is measured by the clarity of ownership across them.
When leaders can see responsibility as clearly as they see infrastructure, governance strengthens naturally.
Orphaned accounts stop being silent risks.
They become decisions waiting to be made.