Cloud security policies define how infrastructure should behave.
They establish access controls, network boundaries, compliance requirements, and operational guardrails. When implemented correctly, these policies help organizations maintain secure and compliant cloud environments.
However, defining policies is only part of the challenge.
Ensuring that infrastructure actually follows those policies is significantly harder.
The Gap Between Policy and Reality
In traditional IT environments, infrastructure changes occurred slowly. Systems were provisioned manually and updated infrequently.
This slower pace made it easier for policies and infrastructure configurations to remain aligned.
Cloud environments operate differently.
New resources are created continuously.
Deployment pipelines introduce frequent changes.
Services scale automatically in response to demand.
With this level of change velocity, infrastructure evolves rapidly.
Security policies, however, often remain static documents or configuration templates. Over time, the gap between policy definition and infrastructure behavior grows.
How Policy Drift Appears
Policy misalignment rarely begins with major security failures.
Instead, it starts with small operational adjustments.
An engineer temporarily expands a permission during troubleshooting.
A deployment introduces a new service that inherits broader access rights.
A network rule changes to accommodate a new dependency.
Individually, these changes appear harmless.
But when they accumulate, the infrastructure no longer reflects the original policy intent. The environment becomes harder to audit and reason about.
Why Traditional Monitoring Falls Short
Most security monitoring tools detect policy violations by analyzing configuration states.
They generate alerts when a rule is broken.
While these alerts are useful, they often lack architectural context.
Security teams see individual violations but struggle to understand how those violations relate to the broader system.
Questions remain unanswered:
Which resources depend on the affected component?
Which policy governs the infrastructure segment?
How did the misalignment emerge over time?
Without this context, resolving violations requires manual investigation.
Policy Visibility as an Architectural Layer
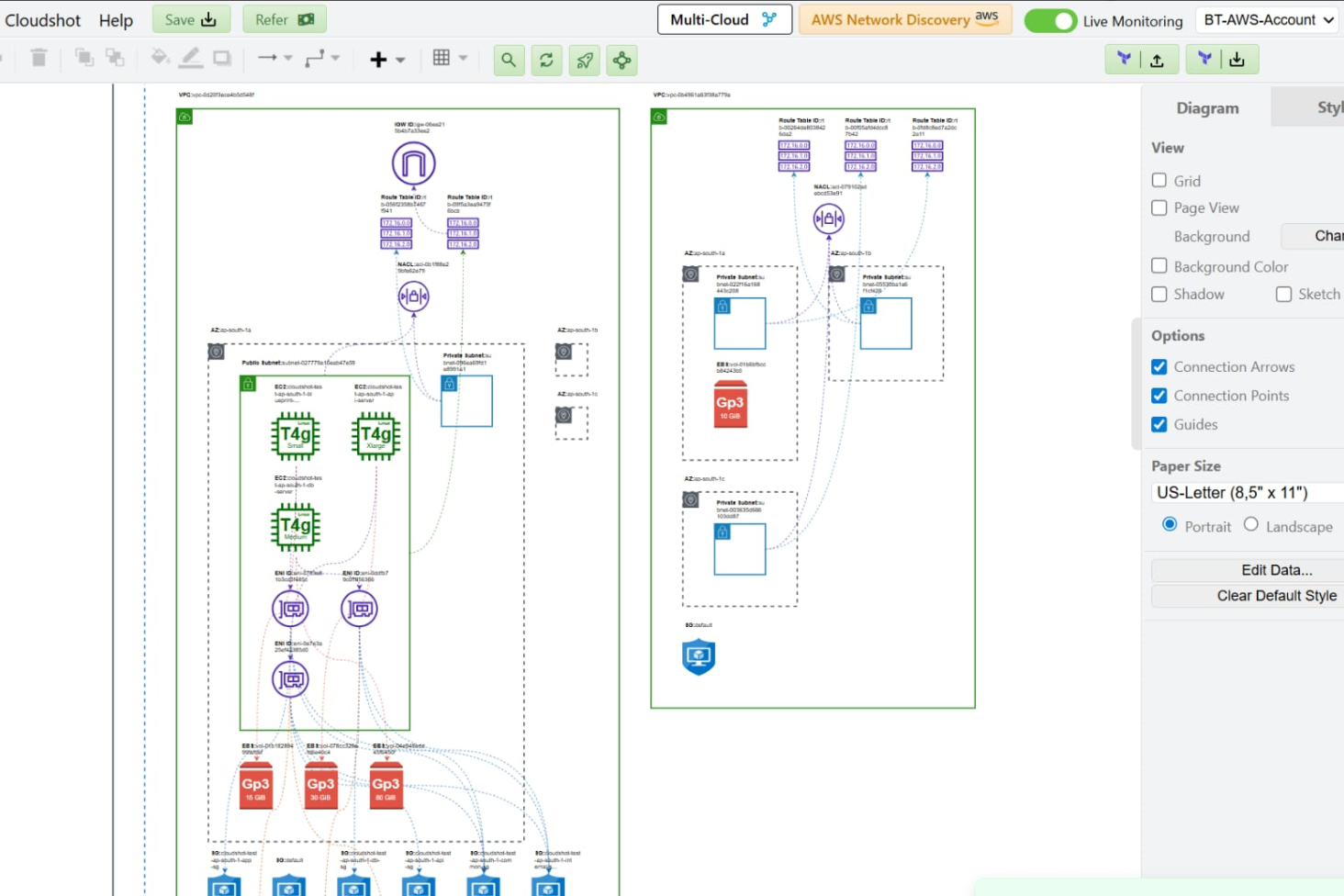
Real-time policy mapping introduces a different approach.
Instead of treating policies and infrastructure separately, it visualizes the relationship between them.
When policies are mapped directly onto infrastructure components, teams can immediately see:
Which policies apply to each resource
Where policy coverage is missing
Where infrastructure changes have created drift
How new services affect existing compliance boundaries
This architectural view transforms how security teams evaluate compliance. Policy becomes visible as part of the system itself.
Operational Security Through Context
When policy alignment is visible in real time, teams can address misconfigurations before they escalate into compliance issues.
Architects can confirm whether new deployments follow policy boundaries.
Security teams can track how permissions evolve.
Compliance teams gain confidence that infrastructure matches documented controls.
Cloudshot enables this visibility by mapping policies directly onto infrastructure relationships. Instead of reviewing policies and infrastructure separately, teams see both within the same operational view. This reduces investigation time and strengthens governance.
From Documentation to Living Policy
Cloud security policies should not exist only as documentation.
They must evolve alongside infrastructure.
Real-time policy mapping helps organizations maintain this alignment.
By visualizing how policies interact with infrastructure components, teams can maintain security posture even as cloud systems change rapidly.