Audit logs are one of the most comprehensive sources of truth in cloud environments.
Every configuration change, access modification, deployment event, and system interaction is recorded in detail.
From a compliance perspective, this level of tracking is essential.
But in practice, audit logs often fail to deliver operational value.
Not because they lack information.
Because they lack usability.
The Illusion of Complete Coverage
Organizations rely on audit logs to ensure traceability.
They provide a detailed record of system activity, enabling teams to investigate incidents and demonstrate compliance.
On paper, this creates confidence.
Every action is logged.
Nothing is missed.
However, the presence of logs does not guarantee understanding.
Why Audit Logs Go Unused
Audit logs are designed for machines.
They capture granular events with precise timestamps and technical metadata.
For humans, this level of detail can be overwhelming.
A single incident may involve thousands of log entries across multiple services.
Security teams must search for relevant events.
DevOps teams must correlate logs with deployment timelines.
Compliance teams must reconstruct sequences manually.
This process is time-consuming and error-prone.
As a result, logs are often reviewed only after an issue occurs.
The Cost of Delayed Insight
When audit logs are not easily interpretable, organizations operate in a reactive mode.
Misconfigurations remain unnoticed.
Unauthorized access persists longer than expected.
Configuration drift accumulates over time.
By the time an issue is identified, the window of exposure has already expanded.
The risk is not that logs are missing.
It is that insights are delayed.
From Logs to Narratives
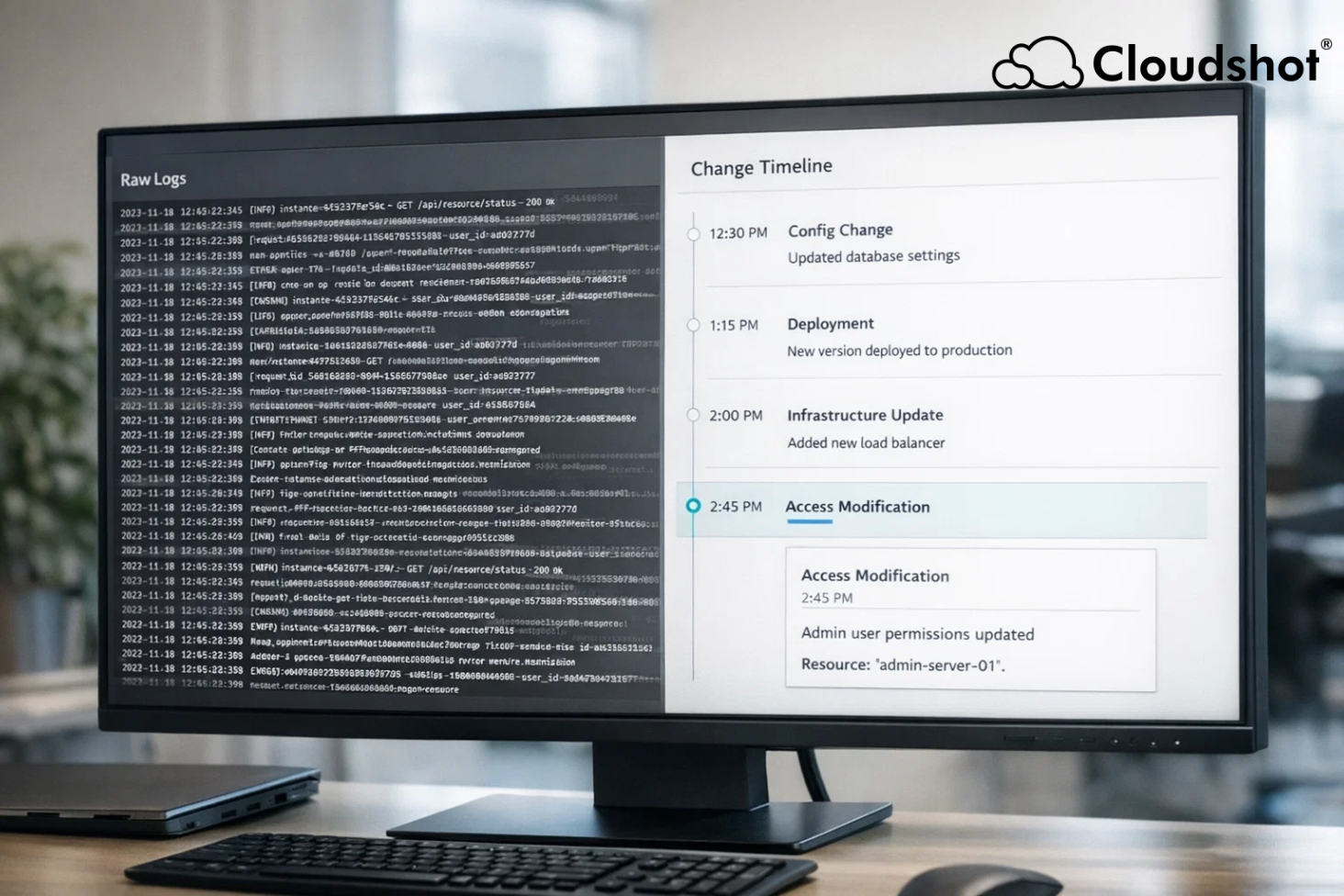
To be operationally useful, audit data must be transformed into readable narratives.
Teams need to see:
What changed
Who initiated the change
When it occurred
How it affected the system
This requires connecting events across multiple layers of infrastructure.
Instead of isolated entries, teams need a continuous sequence.
A change story.
Making Audit Data Actionable
Readable audit trails reduce investigation time.
They allow teams to identify issues earlier.
They improve collaboration between security, DevOps, and compliance functions.
Cloudshot addresses this by reconstructing audit logs into unified timelines.
Instead of navigating multiple tools, teams view a single narrative that connects events across infrastructure, IAM, and deployments.
This transforms audit logs from passive records into active operational tools.
Closing the Visibility Gap
Audit logs are essential.
But their value depends on how quickly teams can extract meaning from them.
Organizations that rely solely on raw logs often struggle to respond efficiently.
Those that convert logs into readable narratives operate with greater clarity.
Conclusion
Audit logs provide data.
Narratives provide understanding.
Without interpretation, logs remain underutilized.
With clarity, they become powerful tools for security and governance.