This week, the cloud stopped being three separate networks and started becoming one. Two major interconnect announcements landed within 48 hours of each other. And while hyperscalers are building highways between their clouds, most enterprise teams still cannot see what is running on one cloud, let alone all of them.
The gap between infrastructure velocity and governance maturity just got wider.
🌩 This Week's 3 Signals (All From This Week Only)
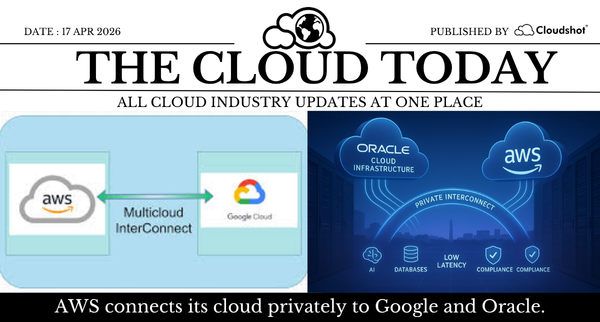
AWS announces general availability of AWS Interconnect multicloud starting with Google Cloud (AWS)
AWS Interconnect multicloud is now generally available, giving enterprises a private managed connection between AWS and GCP across five region pairs. Azure and OCI follow later in 2026. Traffic runs entirely over the AWS backbone, never the public internet. MACsec encryption is on by default.
Why it matters:
Every new private cross-cloud path is a new data flow your security and cost teams need to track. Most teams cannot map what crosses their cloud boundary today. This makes it harder.
Action to be taken:
Audit every cross-cloud data flow before this goes into production. Document which workloads cross between AWS and GCP, who owns them, and what the cost attribution looks like on both sides.
Oracle and AWS establish private high-speed interconnect between OCI and AWS infrastructure (Oracle)
Oracle announced on 16 April that OCI and AWS will be connected via a private high-speed link using Oracle Interconnect and AWS Interconnect multicloud. First rollout is in AWS US East N. Virginia later this year. Oracle already has interconnects with Azure and GCP. Oracle shares rose 4% on the announcement.
Why it matters:
Oracle databases sit in the backend of a large portion of enterprise production systems. As workloads span OCI and AWS natively, the blast radius of a misconfiguration or untracked cost anomaly now grows across both providers at once.
Action to be taken:
If your stack includes Oracle databases alongside AWS, map the new data paths now. Assign a cost owner and a security owner to every cross-cloud dependency before the interconnect goes live.
AWS launches Agent Registry to govern AI agent sprawl across enterprise cloud environments (AWS)
AWS launched Agent Registry in preview this week as part of Amazon Bedrock AgentCore. It gives enterprises a centralized catalog to discover, govern, and reuse AI agents across AWS, other clouds, and on-premises. A Gartner survey found 58% of large enterprises have deployed AI agents in production but only 12% have formal governance frameworks covering them.
Why it matters:
AI agents are the new untagged resources. Deployed fast, without ownership metadata, without cost attribution, without audit trails. The same visibility gap that creates zombie EC2 instances is now creating agents with access to production databases and financial systems.
Action to be taken:
Inventory every AI agent your team deployed in the last six months. For each one, document the owner, the cloud resources it touches, the permissions it holds, and what it costs to run.
💡 Cloudshot Tip of the Week
This week's announcements share one root problem: infrastructure is connecting faster than governance can track it.
New cloud interconnects mean new data paths. New AI agents mean new access patterns. Both create new cost and security exposure the moment they go live.
The question to ask your team this week is simple. If a new cross-cloud data flow goes live today, how long before your security team sees it? How long before your cost team can attribute it? If the answer is days or weeks, the interconnect is not your problem. The visibility gap is.
Cloudshot maps live architecture, IAM access, and cost attribution across AWS, Azure, GCP, and OCI in one view. New paths surface immediately. New agents can be tracked. Unattributed spend flags before the invoice arrives.
🗓 What We Published This Week
13 Apr (Mon). Your cloud bill is not a finance problem.
Cost overruns start in architecture and tagging, not Finance. The fix starts at deployment, not at the end of the month. Full article linked in comments.
→ Full Article15 Apr (Wed). A ₹40K spike. Nobody knew why. Here is what actually happened.
One EC2 cluster. Six weeks of undetected spend. Three days to trace what Finance needed in four hours. Full article linked in comments.
→ Full Article🔭 Strategic Signal
This week closed with a clear signal for every CTO running multi-cloud.
The infrastructure layer is consolidating. Clouds are connecting to each other directly. AI agents are running across all of them. The teams that build unified visibility now will be able to govern this. The teams waiting for their tools to catch up will find out what they missed from an audit or an incident.
Q2 is the window. After that, it is damage control.
⚠️ Before it happens to you...
Pick your most business-critical cross-cloud workload this week. Trace it end to end across every cloud it touches. Count the IAM roles, the data flows, the cost centers, and the agents that interact with it.
If that takes more than 15 minutes, you do not have visibility. You have dashboards.
Keep your visibility sharp. The cloud is no longer where it used to be.